# SCIM - Azure
### Supported Features
* **Push Users** Users created in Azure will also be created in Couchdrop
* **Push User Updates** User updates in Azure will be pushed to the corresponding users in Couchdrop
* **User deactivation** Users deactivated in Azure will be deactivated in Couchdrop
* **Push Groups** Groups created in Azure will also be created in Couchdrop
* **Push Group updates** Group updates in Azure will be pushed to the corresponding users in Couchdrop
* **Group deactivation** Groups deactivated in Azure will be deactivated in Couchdrop
### Configuration Steps
#### Create User Provisioning Token in Couchdrop
Navigate to [User Provisioning](https://my.couchdrop.io/manage/settings/userProvisioning) in Couchdrop’s interface and **create a new Provisioning Token**. This will be used in the Azure Active Directory provisioning process.
#### Configure Enterprise Application in Azure Active Directory
Navigate to your [Administration dashboard](https://aad.portal.azure.com/#blade/Microsoft_AAD_IAM/AppGalleryBladeV2) in Microsoft’s admin portal and **create an enterprise application.**
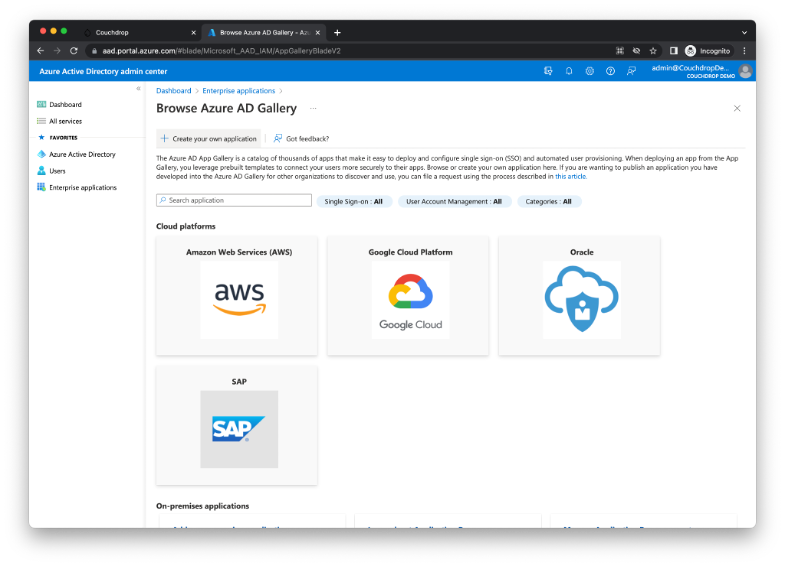
Provide a name for the application and select “Integrate any other application you don’t find in the gallery (Non-gallery)
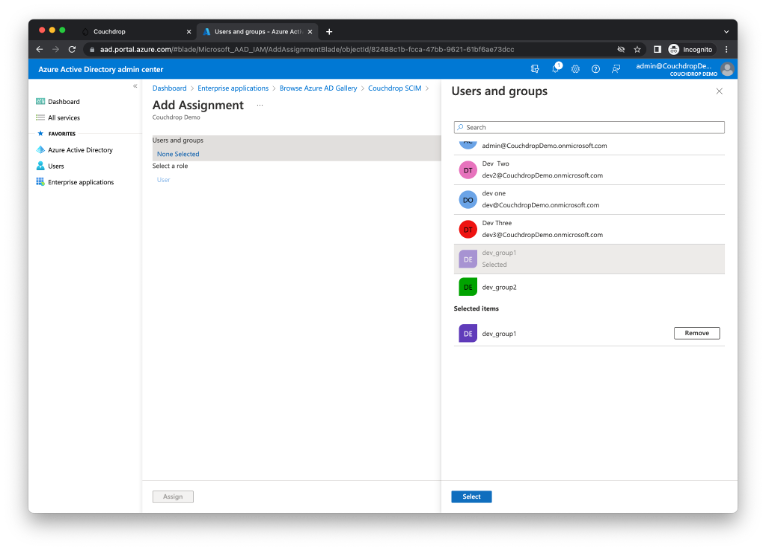
Next assign users and groups to the newly created application that you would like to have provisioned in Couchdrop.
Select **Add user/group**
Select the desired users or groups that should be provisioned through to Couchdrop then **Select** and **Assign**.
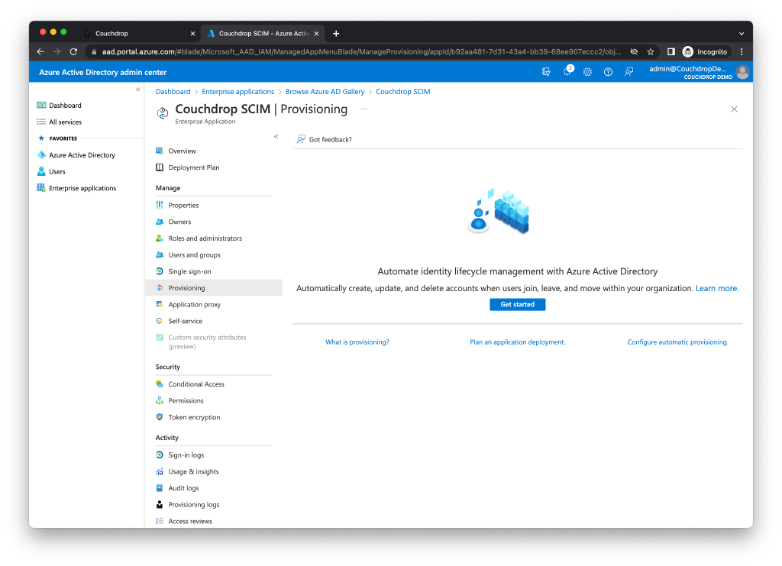
#### Configure SCIM provisioning between Azure Active Directory and Couchdrop
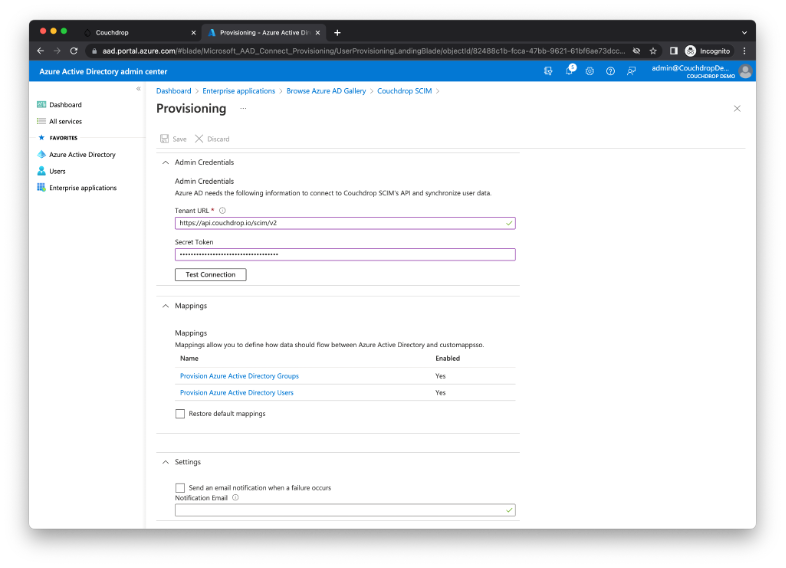
Navigate to the **Provisioning Tab** on the left hand side. Next select **Get started** to configure the tenant URL and the User Provisioning Token that was created in **Step 1**. Provisioning mode should be set to automatic. The Tenant URL is: .
Select **Test Connection** and Azure will attempt to connect as well and vwill retrieve schema information needed for the user and group mapping. If tested successfully then select **Save**.
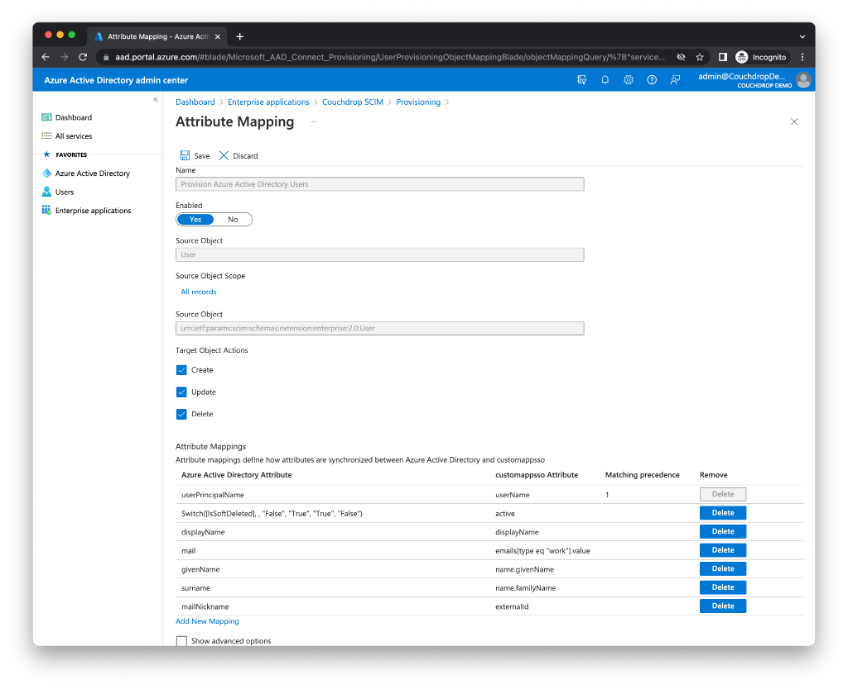
#### Configure user mapping
Select **Provision Azure Active Directory Users** as required.
Couchdrop requires the following user SCIM attributes for the SCIM system to be mapped, all others should be removed.
| **Custom Application SSO Attribute** |
| ------------------------------------ |
| userName |
| active |
| emails\[type eq "work"].value |
| name.givenName |
| name.familyName |
| externalId |
The **externalId** attribute may need to be remapped from **mailNickname** to **objectId** on the Azure Active Directory attribute side depending on your settings.
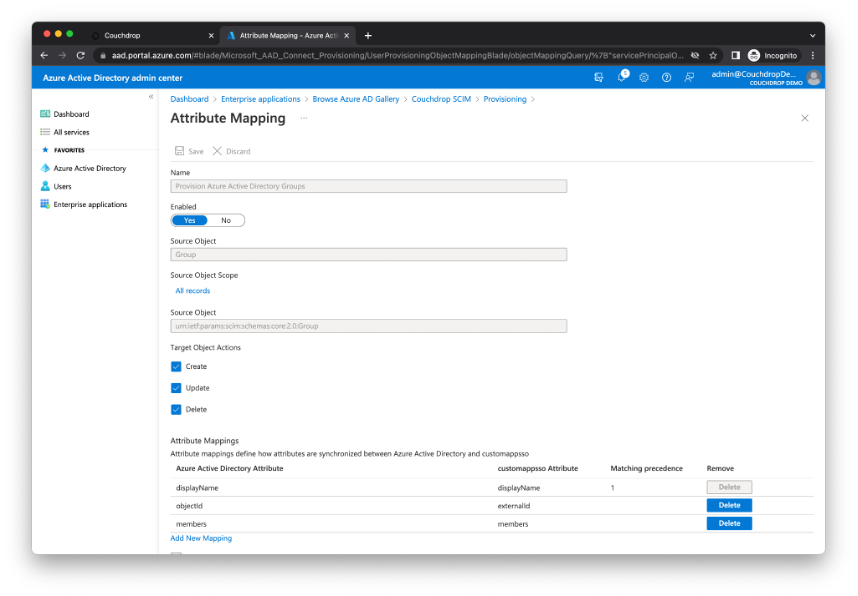
#### Configure group mapping
Select **Provision Azure Active Directory Groups** as required.
Couchdrop requires the following user SCIM attributes for the SCIM system to be mapped.
| **Custom Application SSO Attribute** |
| ------------------------------------ |
| displayName |
| externalId |
| members |
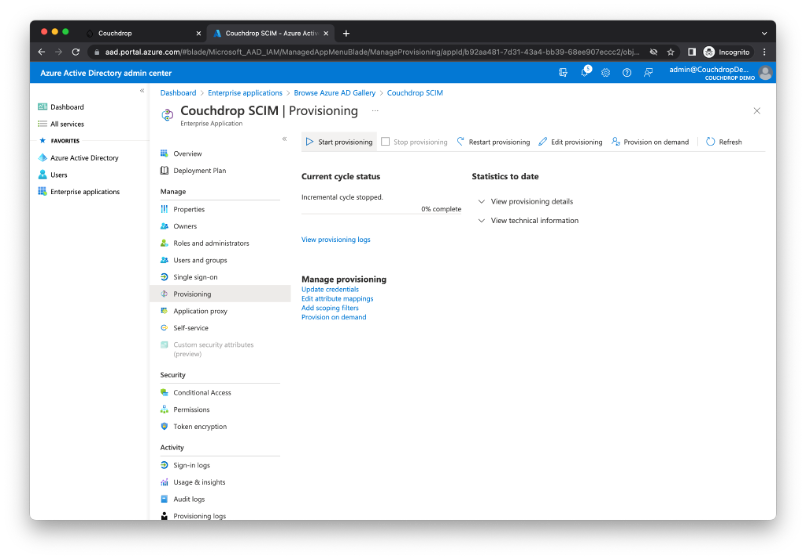
#### Start the user and group provisioning process
Navigate back to the custom application breadcrumb (in this case it’s Couchdrop SCIM) and to **Provisioning**. From here select the **Start provisioning** button.
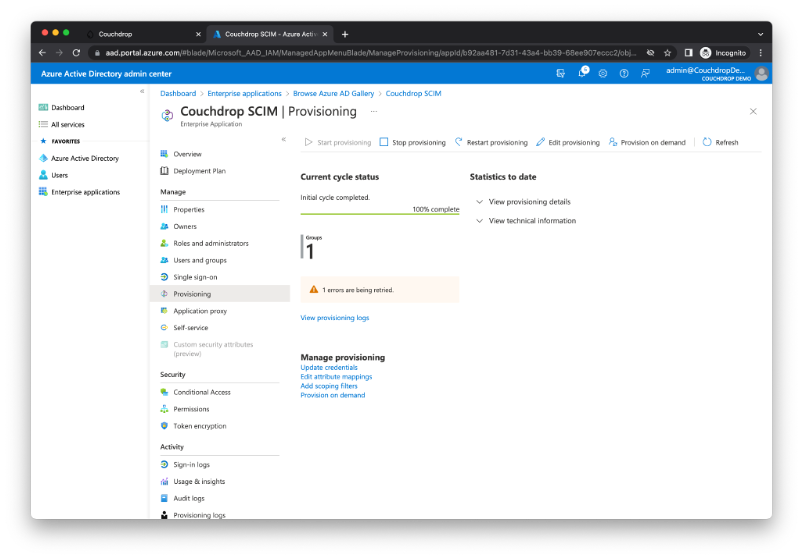
After the provisioning has completed running the first time a status should be required that indicates how many users and groups were provisioned within the Couchdrop product. Further information can be located by selecting **View provisioning logs.**
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://docs.couchdrop.io/administration/sso-and-single-sign-on/scim-azure.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.